Per http://zitstif.no-ip.org/?p=1240, I thought it would be a good idea to try to make another version of this flash drive but one that supports UEFI. Personally, I still like BIOS even though it has its limitations but UEFI is the wave of the future. Take note that the bootable flash drive needs to have secure boot disabled. Additionally, this flash drive is not meant to replace the original zitUSB. (URL to download is toward the bottom of the post).
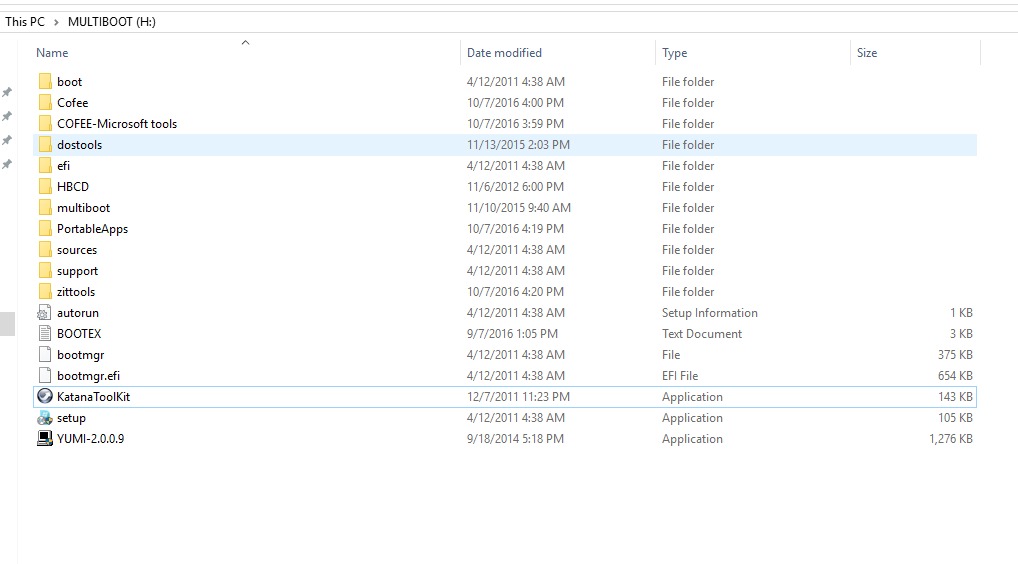
Here’s the root of the flash drive:
Here is the `tree` of the drive: http://zitstif.no-ip.org/usbUEFI/tree.txt
Here’s a list of the distros/bootable OSes:
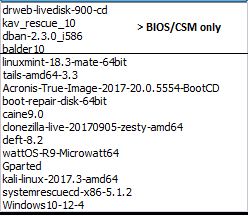
The first four will only work with BIOS/CSM mode. Additionally, this bootable flash drive isn’t perfect. Some UEFI systems result in this:

The only way to get it to boot under this condition is to turn CSM/legacy mode. Other limitations include: no memory testing utilities (memtest or the like), no Hiren’s BootCD, no UBCD, or Windows 7 installer. As a quasi workaround for Hiren or UBCD like utilities, you can boot into balder10 (FreeDOS) and use DOS tools that are located under C:\DOSTools\(FreeDOS starts on A:):
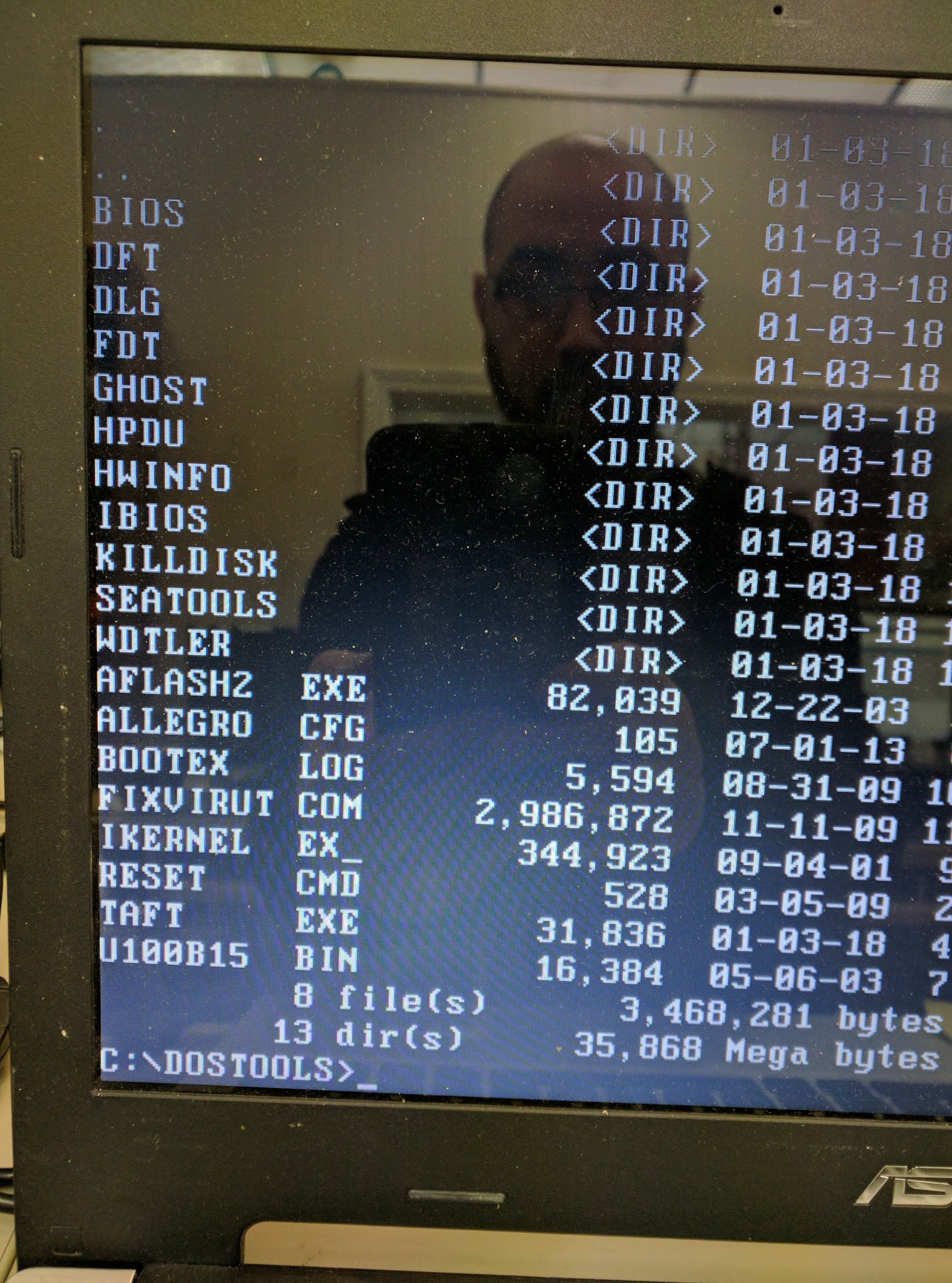
There are no password cracking or clearing tools per se (like passcape), but Kali Linux should suit most of these needs.
TAKE NOTE THAT YUMI-UEFI-0.0.0.6 IS ON THE ROOT OF THE DRIVE, USE THIS VERSION FOR ADDING OR REMOVING DISTROS! IF YOU USE ANY VERSION DIFFERENT TO ADD OR REMOVE DISTROS, YOU WILL POTENTIALLY MAKE YOUR FLASH DRIVE UNBOOTABLE!
I made an image of my flash drive using clone-zilla-2.4.2-61-i686-pae, however that version or any newer version should work in creating your flash drive.
I am able to boot off of this flash drive using a Macbook (13-inch, Late 2009) without having to use Plop.
Requirements:
- 1 Flash drive that is 64GB or larger
- A computer with working USB ports
- clone-zilla-2.4.2-61-i686-pae or newer and know-how for using clonezilla to restore an image (look here if needed)
- patience to download a 20GB file
- To use: a computer that can either be BIOS/legacy or UEFI, if UEFI, then secure boot needs to be disabled. System needs to be x64, ARM IS NOT SUPPORTED
Hashes:
zitstif-multiboot-usb-yumi-uefi-0.0.0.6-2018-01-04-17-img.rar
MD5: ee4f4c6d71332ef501960c55c6fd2702
SHA-1: e8d03189e0ab487aa3bc079b062315ec3d1f295c
Contents of rar archive:
MD5 SHA-1
————————————————————————-
c4eb71e8c57467fd842da72d6cb296f8 d24ffae736a23a611287f74ff5d98190db177046 blkdev.list
MD5 SHA-1
————————————————————————-
0a2b1205457eb388c51b31a45a06512e a1565d84e641c570a32a078bc2a50c1289d6f401 blkid.list
MD5 SHA-1
————————————————————————-
ed3757d3f740c038ba403f3543eef309 b573883b5b0a87004c6538c9ae00d57286bb894f clonezilla-img
MD5 SHA-1
————————————————————————-
60c92cb5ae1024b13cbbedb24588a5e8 eab6a5a6fe327e1aee0edb3173d35db0d6e55dd5 dev-fs.list
MD5 SHA-1
————————————————————————-
84f6bf10d84c171a2630a153ac12411b 8fdca4e3395cc1b00dcc5438212ce344f7873a8f disk
MD5 SHA-1
————————————————————————-
55dadb9b2c114d2ceee297ab803ac9dc 5c1f5da37633b6beb01aca124fbba8cfba315463 info-dmi.txt
MD5 SHA-1
————————————————————————-
3367baf790c137e1df89e3f48511b3cd 3078afe6ab9f8842ef7741ea1c1658fc4f94505d info-lshw.txt
MD5 SHA-1
————————————————————————-
42c2b29d859f7763d33df26ff3892977 631c8f0db755d2ee6251c9b7d01c202bfe7444f6 info-lspci.txt
MD5 SHA-1
————————————————————————-
4501bf778509426fba474f19fa0d0cf4 ea33bed911e69784fe550c7e062edf8b4263a648 info-packages.txt
MD5 SHA-1
————————————————————————-
5459baead8a74ed82df038ee42aaa0fe 943a89a635e752eede455ec312145a3f89df3748 info-saved-by-cmd.txt
MD5 SHA-1
————————————————————————-
4988b9e1d22f981cc09ebdfaf374da5b bb60b4ce7dfbb0d09e87c2c0aa13d36d9ae3f249 parts
MD5 SHA-1
————————————————————————-
fc00b4095d38499a5c564cc23f9e6f29 7a67e1d4ad2383c06b206bdcc3c05b08170e184a sda-chs.sf
MD5 SHA-1
————————————————————————-
ed356b009be474fef10efc60939de511 bfa8f7bae00715fb462198b3f9a6dcec0d8ed4d8 sda-hidden-data-after-mbr
MD5 SHA-1
————————————————————————-
7ee1f53bf0a1f5f79917e30da9c831c9 2286e00fa9738a2e5c98eaa234cbbdc589a40962 sda-mbr
MD5 SHA-1
————————————————————————-
2ec3808d83d88296f4cfc3aee315cdfc 06d33797d9a5b4db9c3cc73aef865b827e8eea85 sda-pt.parted
MD5 SHA-1
————————————————————————-
9c65b62f3539e9fdcf239753282458f5 a9974b1fc2d537b445b127ec4e30e52844fe0b16 sda-pt.parted.compact
MD5 SHA-1
————————————————————————-
9d18933aa845f01293a4080ce26e4957 803139ec7bf73cc404d9ebce5716cceaf05bfb85 sda-pt.sf
MD5 SHA-1
————————————————————————-
53bc4c570d657b342b8d758a84d52df4 71659410753ade5d22d200097b8a5ea1fcd77a16 sda1.vfat-ptcl-img.gz.aa
MD5 SHA-1
————————————————————————-
adbaec9fb7898d6ded83451b28b7c673 2dcb2789a17868218731d864b9e423451633c8b7 sda1.vfat-ptcl-img.gz.ab
MD5 SHA-1
————————————————————————-
66921c23d30fe2c790dca00014830dd3 018fa0b21de3aaa78b37133e7597e405a495a1f8 sda1.vfat-ptcl-img.gz.ac
MD5 SHA-1
————————————————————————-
2233bd350443971905318d97f26f46dc bd3f7378b3caee83f6eb21853d6f9d11ea5a5105 sda1.vfat-ptcl-img.gz.ad
MD5 SHA-1
————————————————————————-
0b48065e0a1ad87cdfb1ca63f610ca69 362ca476c881cfdeb568297304d6e4e4d53f5949 sda1.vfat-ptcl-img.gz.ae
MD5 SHA-1
————————————————————————-
111f63040c1a5a7fb8a74ed17713b5c1 8f9bb1e8ae0d977c0063fa10ff6e470b5f7b9678 sda1.vfat-ptcl-img.gz.af
Download:
File is hosted on Google Drive:
http://zitstif.no-ip.org/usbUEFI/url.txt
sha1sum 244011a931e5abf1078ba46b3338f3091fe83637
Feel free to leave any feedback.