There’s something about Apple computers that I like to pick on. It’s not really the computers per se, it’s mostly the end users who can get on my nerves. Most people who I’ve met that use Apple computers, have little to no knowledge about computers or information technology. Yet, at times, these people tend to get lofty because they use Apple Computers and feel as if they can be be smug towards you since you might not own an over priced PC. (An Apple computer, which I’ll explain).
Now, not all Apple computer users are this way, and I actually have a few friends who are huge computer enthusiasts, whom use Apple computers and are very knowledgeable in the field of information technology. Also, don’t mind if I meander, but if an Apple computer is a ‘computer’ and if you consider it personal to you.. then isn’t it technically a ‘PC’. as in personal computer? 🙂
With that aside, I’m reintroducing a bash shell script that one can use in a LAN to identify Apple computer users. I’ve tested it on Ubuntu and Backtrack and have had great results. As a matter of fact, a while ago I wrote this program, but as times have changed and the output of nmap has changed, I needed to rewrite this shell script.
Features of NameThatApple (nta):
Information discovery — finding the names of Apple computers which 90% of the time have their real name in the title.
Port scanning — this does a limited number of port scans on ports that are usually open on Apple computers
Iphone/Ipod touch jail break test — If port 22 is discovered, a python script relying on pexpect will test to see if the default password for the root account is ‘alpine’.
MAC address discovery — nta will ARP the Apple computer and report back the MAC address.
If you have problems resolving the host names of the Apple comptuers with my program, make sure your Linux distro supports MDNS and/or you may have to try a different version of netcat.
If you have any other problems, please contact me or leave a comment.
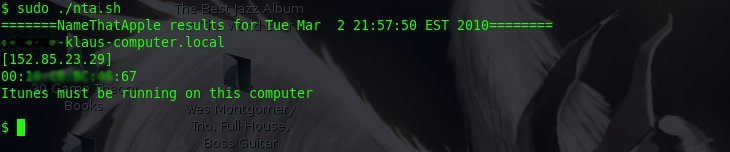
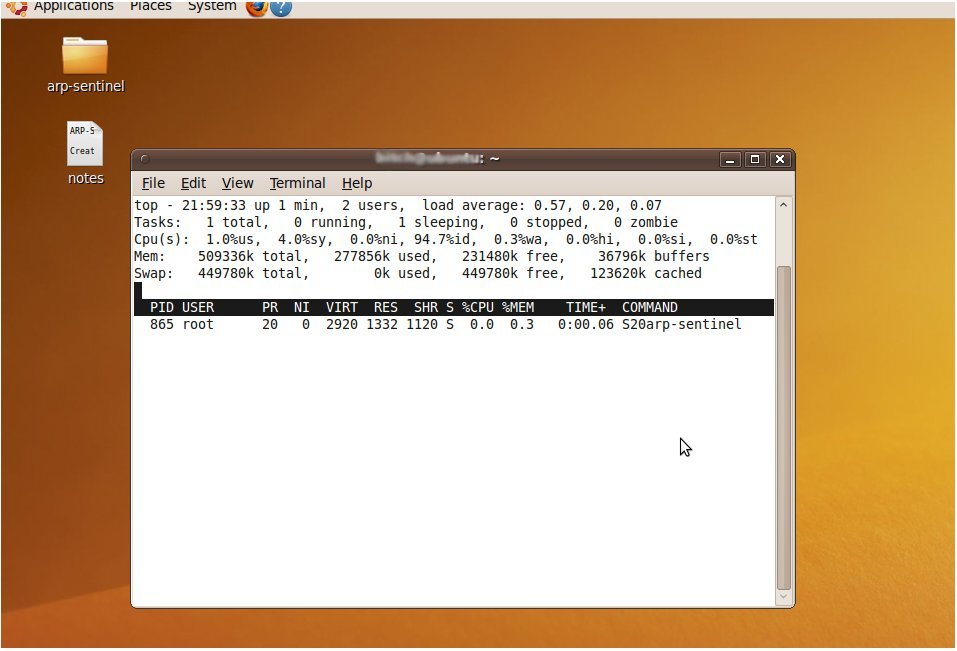
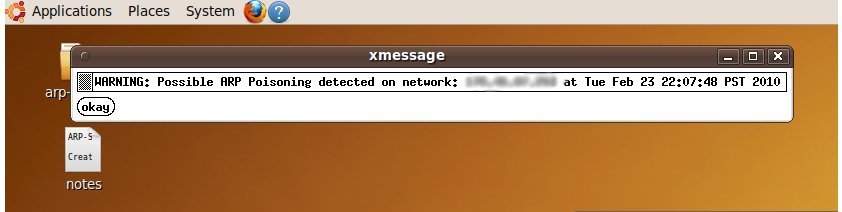
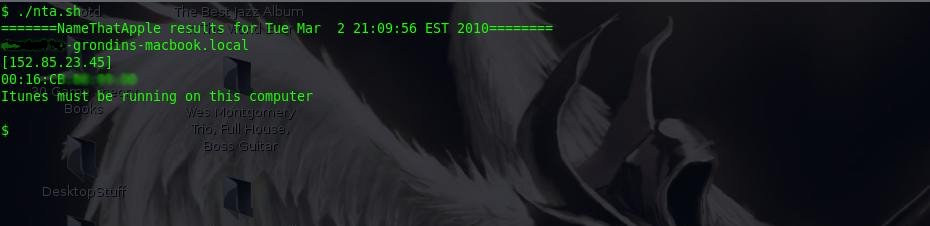
Here’s some screen shots of nta.sh in action: (Note: I blurred the end users names out for privacy)
If you want to capture the out put of nta.sh, then pipe the output to ‘tee’, like this:
sudo ./nta.sh | tee newlog.log
Here are the files:
Plain text (main shell script):
http://zitstif.no-ip.org/nta/nta.txt
Plain text (jail break test script):
http://zitstif.no-ip.org/nta/jailbreaktest.txt
Tar file (both files):
http://zitstif.no-ip.org/nta/nta.tar
MD5sum: 0e4672083861d00893afa9d9f0527574
As always, more to come! I’m planning on adding more features to nta.sh, such as having it interface through some means with metasploit.